Release 10.32.2
March 03, 2025
What’s New?
Update: User Interface (UI 4.0) of the Qualys Enterprise TruRisk™ Platform
Automatic UI 4.0 Upgrade with Rollback Option
We rolled out our newly designed user interface (UI) for the entire platform in the latter half of January 2025! This update introduced a consistent and streamlined experience across all applications simultaneously, ensuring that navigation and functionality are more intuitive than ever. As part of this transition, the new UI 4.0 will become the default interface when you log in.
We are implementing this transition in phases to ensure a smooth experience for all users. To stay updated on the rollout schedule for UI 4.0 Phase 2, subscribe to the Qualys Status page.
Existing customers can temporarily toggle back to the previous interface for next 60 days if needed. However, the new subscribers will automatically access UI 4.0 without this option.
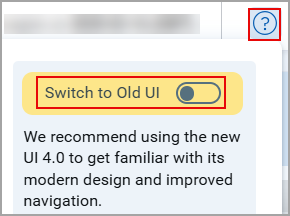
The toggle switch to swap between the new and old UI is located under the Help menu in the top navigation bar.
Check out our blog for tips on planning your transition.
Qualys Vulnerability Management (VM)
Download List of IPs for Tracking Consistency Check
With this release, we have introduced a Download option in the Tracking Consistency Check window, allowing you to retrieve the complete list of IPs. The Tracking Consistency Check window displays up to 100 IPs, with the remaining IPs not displayed.
To download the list of IPs navigate to Assets > Address Management > Select the required Network > Filters > Select Check IP Tracking / Check DNS Tracking / Check NetBIOS Tracking > Download
![]()
With the addition of the Download option, you can download the complete list of IPs (including the ones not displayed in the Tracking Consistency Check window) in an Excel file (CSV format).
![]()
Qualys Policy Compliance (PC)
New UDC Technology Support for Debian 12 and Windows 2025 Server
In this release, we have added new User Defined Control (UDC) technology support for Debian 12 and Windows 2025 Server. You can now create a new UDC where you can select and use Debian 12 and Windows 2025 Server under Control Technologies.
Create New UDC for Debian 12
The basic flow to create a new User Defined Control (UDC) for Debian 12 using new control technology support is as follows:
- Navigate to Policies > Controls. Here we provide many controls for you to choose from and create your own UDCs.
- Click New > Controls.
The New Control window is displayed. - In the left pane, select Unix Control Types.
- Select a control type from Unix Control Types list.
- Under Control Technologies, select Debian GNU/Linux 12.x from the list and provide the mandatory information.
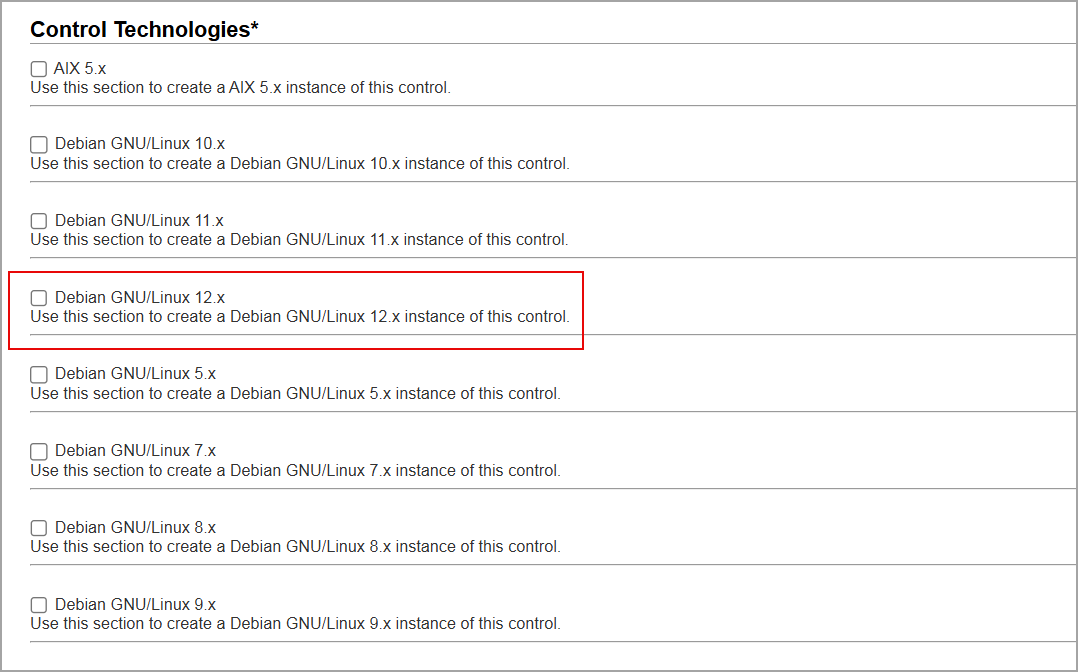
- Click Create.
The new UDC with support for Debian 12 is created.
Create New UDC for Windows 2025 Server
The basic flow to create a new User Defined Control (UDC) for Windows 2025 Server using new control technology support is as follows:
- Navigate to Policies > Controls. Here we provide many controls for you to choose from and create your own UDCs.
- Click New > Controls.
The New Control window is displayed. - In the left pane, select Windows Control Types.
- Select a control type from Windows Control Types list.
- Under Control Technologies, select Windows 2025 Server from the list and provide the mandatory information.
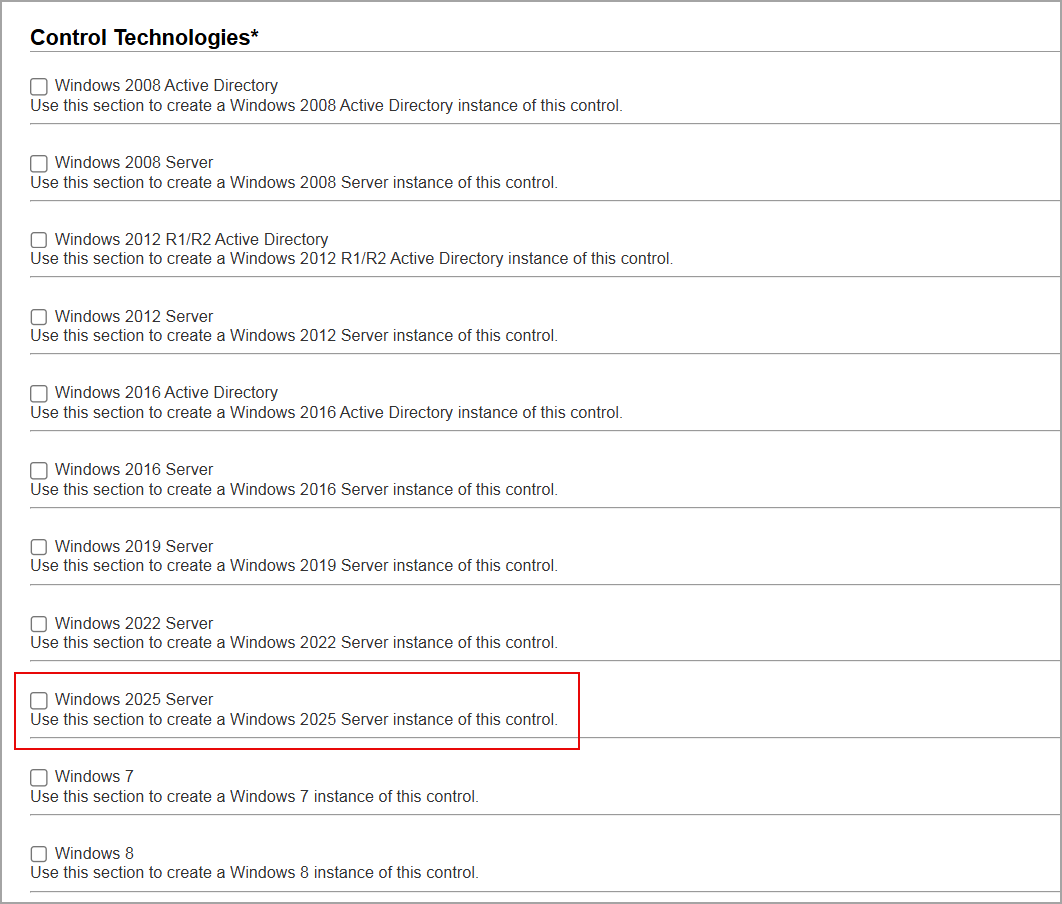
- Click Create.
The new UDC with support for Windows 2025 Server is created.
Issues Addressed
The following reported and notable customer issues have been fixed in this release:
| Component/Category | Application |
Description |
| VM - Option Profile | Vulnerability Management | When the users selected the Custom option in the Overall Performance field under Configure Scan Performance Settings, the count for Hosts to Scan in Parallel for Scanner Appliances was displayed as a maximum of 70 in spite of setting the count to 99. Relevant code changes have been made to fix the issue. |
| VM - Scan Schedule | Vulnerability Management | When the users were configuring the Scheduled EC2 vulnerability scan by selecting Build my list in the Scanner Appliance field, the scheduled scan was not created and also received an incident signature on the User Interface after the setup was completed. Relevant code changes have been made to fix the issue. Relevant code changes have been made to fix the issue. |
| VM - Reports General | Vulnerability Management | When the users downloaded the report in docx format, the links provided in the report were unable to open and were getting an error. Relevant code changes have been made to fix the issue. |
| VM - Host Based Report | Vulnerability Management | When users added a Service to Unauthorized Services (Scan Report Template > Services and Ports > Unauthorized Services) and enabled the General Remote Services category along with other categories under Included Categories Filter in the Scan Report Template, QID 38175 was not detected in the report. The QID was only detected when all categories were selected. Relevant code changes have been made to fix the issue. |
| VM - Scan API | Vulnerability Management | When the users executed a list scan schedules API /API/3.0/fo/schedule/scan/, the fqdn parameter did not work, and some issues were faced. Relevant changes were made to fix the issue. The fqdn parameter now supports only create and update schedule scans. This is documented in the Qualys API (VM/PC): PDF and HTML. |
| VM - UI General | Vulnerability Management | When users viewed the list of IPs in the Tracking Consistency Check window, they could see only up to 100 IPs, with the remaining IPs not displayed. Relevant code changes have been made to resolve this issue. A Download option has been added, allowing users to download an Excel file containing the complete list of IPs. |
| VM - UI General | Vulnerability Management | When users tried to add IPv4 VLANs to appliances with serial numbers above 29000, they encountered an error stating, "You cannot add more than 99 VLANs," despite the maximum limit being set to 4094. Relevant code changes have been made to resolve this issue. |
| PC - API | Vulnerability Management | When the subusers launched policy report based on host ID and instance string with OS, using the API /api/2.0/fo/report/, subusers were getting the output as parameter instance_string has invalid value: os for AGMS account. Relevant code changes have been made to fix the issue. |
| PC - Controls | Policy Compliance | When users selected the Copy to Other Technologies option to copy the control settings from the selected technology to all other technologies listed in the policy for the same control, the control settings were not transferred, and the previously selected options for the technology were also lost. Relevant code changes have been made to fix the issue. |
| PC - Reports | Policy Compliance | When the users performed a policy evaluation, it failed due to a mismatch in apostrophes between the expected and actual control values. To resolve this, users needed to update the expected value to match the actual apostrophe and re-run the evaluation. This behavior was previously not documented. It is now added in the Online Help in the Using the Policy Editor section. |