Enterprise TruRisk™ Platform Release 10.33
April 2, 2025
Qualys Vulnerability Management (VM)
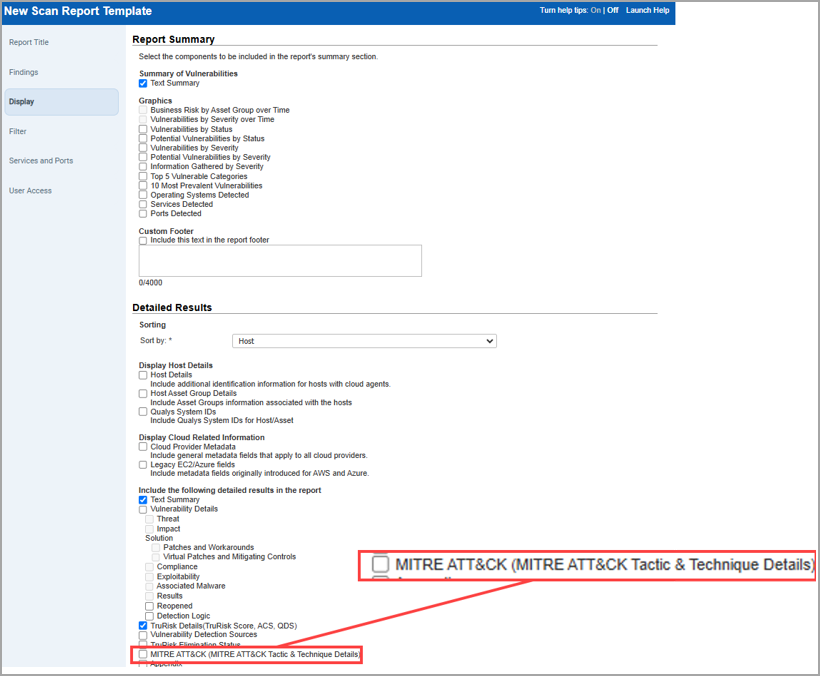
Availability of MITRE ATT&CK in Scan Report Template
With this release, the MITRE ATT&CK tactics and techniques, is now extended to the scan report. This enables you to generate a detailed report that displays the tactic and technique names and IDs in the host-based report. This allows you to take faster remediation actions from an MITRE prioritization perspective. This provides a clear and structured view of how potential or active threats align with known adversary behaviors.
To include MITRE ATT&CK details in the report:
- Navigate to the Reports > Templates tab.
- Click New > Scan Template > Display tab.
- Under Detailed Results > Include the following detailed results in the report > select MITRE ATT&CK (MITRE ATT&CK Tactic and Technique Details).
When you generate a report, you can view the following new columns in CSV report format:
- MITRE ATT&CK Tactic Name
- MITRE ATT&CK Tactic ID
- MITRE ATT&CK Technique Name
- MITRE ATT&CK Technique ID.
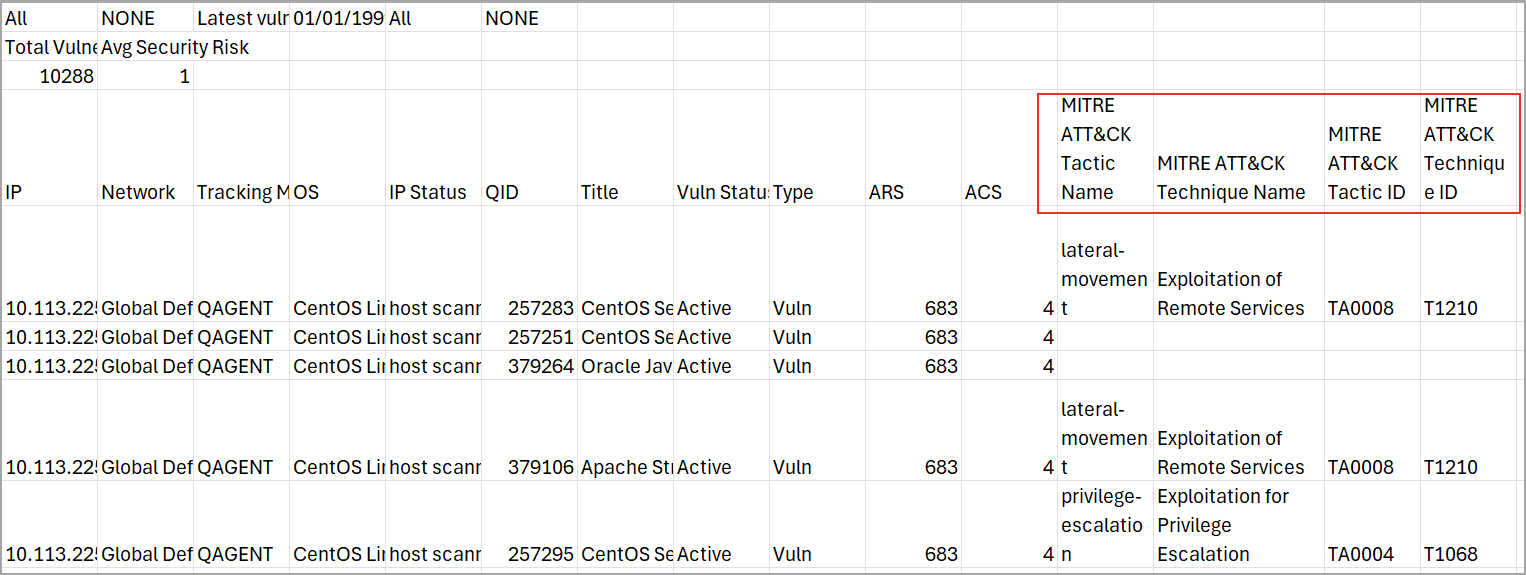
It supports only host-based CSV reports.
For more information on VMDR MITRE ATT&CK Matrix Prioritization, refer here VMDR Help.
Qualys API Support for MITRE ATT&CK
For this enhancement, an updated version of the following APIs are available:
- Scan Template API: /api/3.0/fo/report/template/scan/
- Host Detection List API: /api/4.0/fo/asset/host/vm/detection/
For more information, refer to Enterprise TruRisk platform 10.33 API Release Notes.
Simplified Load Balancer DNS Names Detection for Azure
With this release, we have simplified the process of adding load balancer DNS names when performing a Cloud Perimeter Scan for the cloud provider Microsoft Azure.
Previously, users had to manually enter load balancer DNS names to include them in the scan. Now, users can select the checkboxes, Include Public Load balancers from selected connector and Include Public App Gateway Load balancers and add the load balancer DNS names associated to the selected connector.
To access the checkboxes navigate to Scans > Scans > New > Cloud Perimeter Scan > Target Hosts.
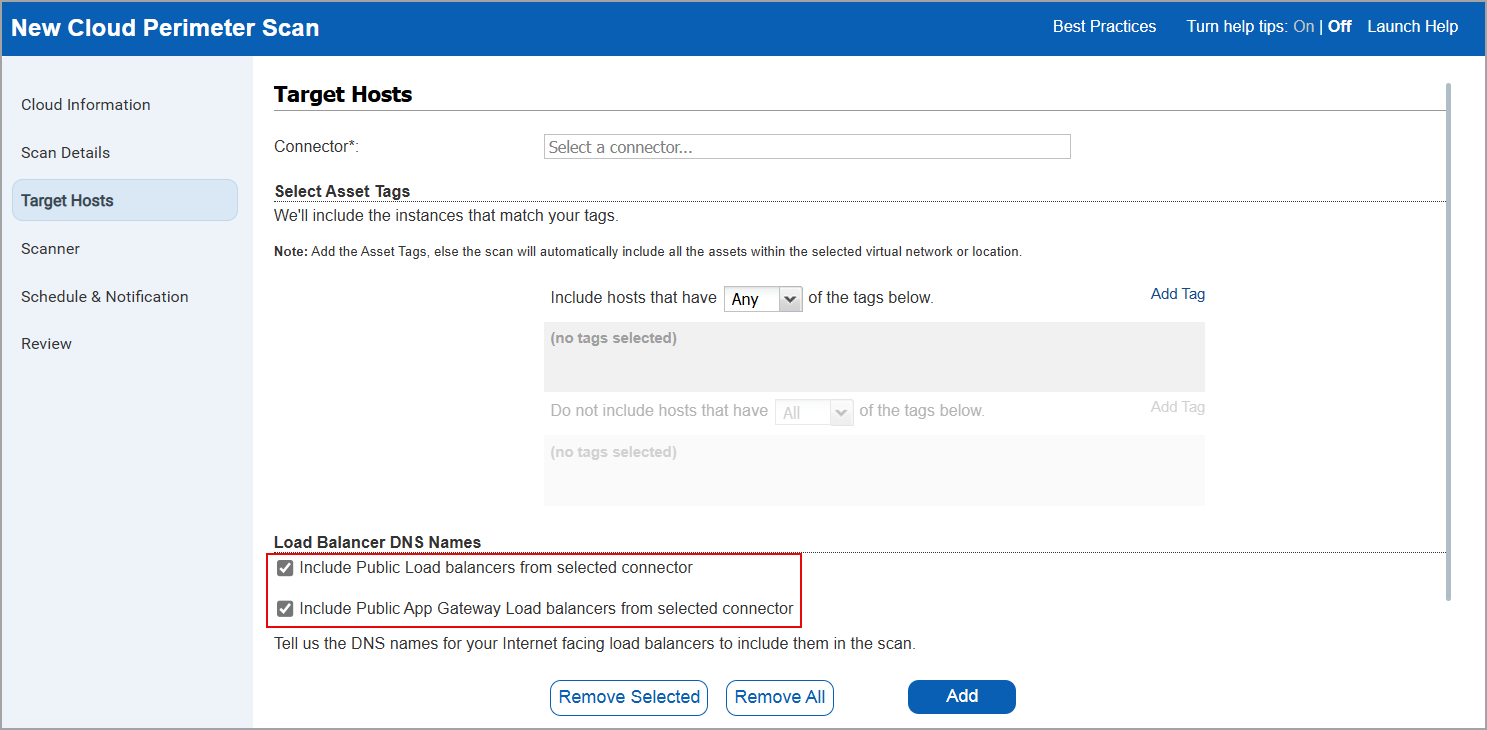
Once these checkboxes are selected, the system automatically retrieves the load balancer DNS names and displays the total count under Target Hosts in the Review tab.
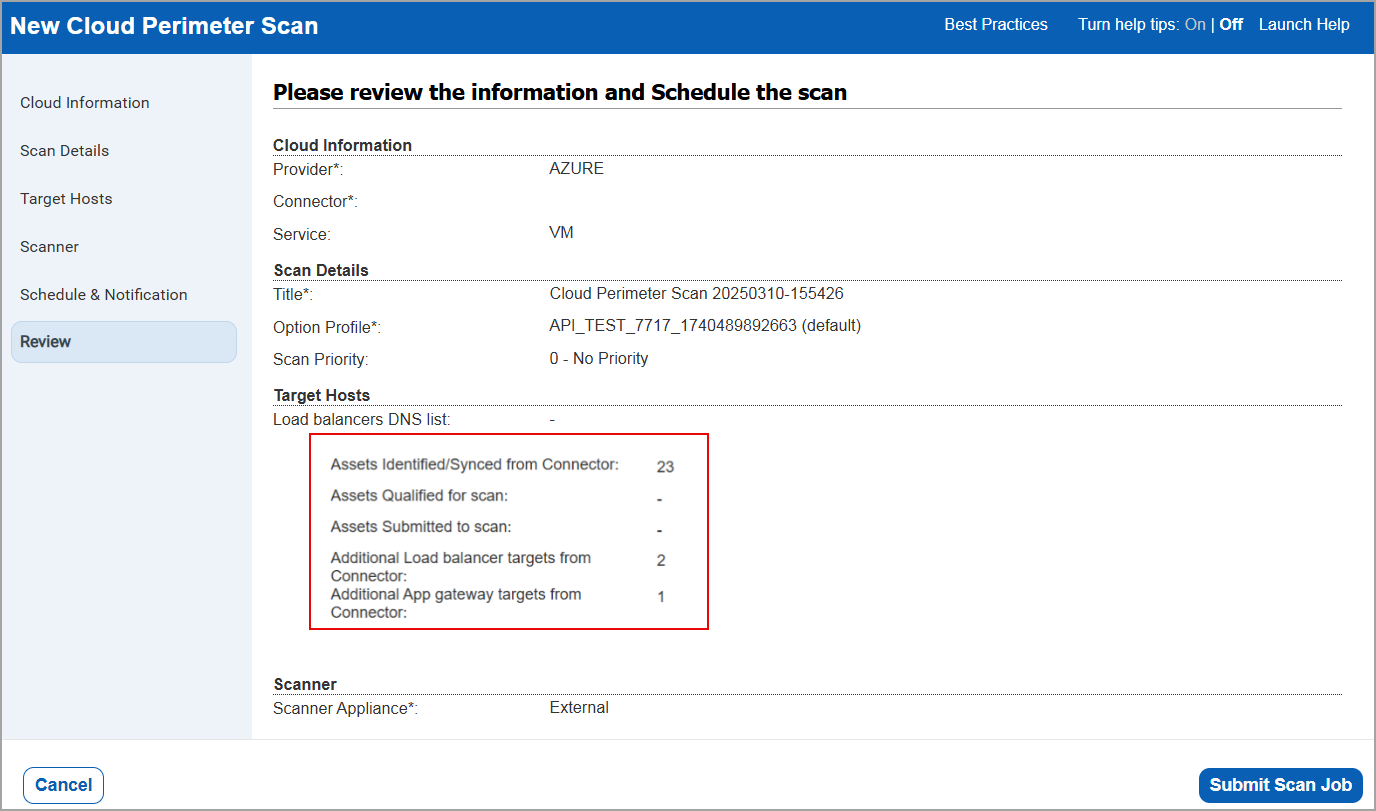
To access the two new checkboxes, users must have the Vulnerability Management Scan Process (VMSP) subscription enabled and access to the TotalCloud (TC) module.
Qualys API Support for Load Balancer DNS Names Detection for Azure
For this enhancement, we have updated an input parameter in the scan/cloud/perimeter/job API. For more information, refer to Enterprise TruRisk platform 10.33 API Release Notes.
Deploy Qualys Cloud Agent Using Qualys Scanner
With this release, you can now deploy Qualys Cloud Agent with the help of Qualys Scanner without relying on third-party tools to deploy the cloud agent. Only the user with a Manager role who is also a primary contact can enable this feature. The scanner can deploy Cloud Agent on Windows/Linux assets that have the following platform types:
- Windows-X86-32/64
- Linux-X64-RPM
- Linux-X64-DEB
Prerequisites
- PC/SCA authentication records (Windows or Unix) should be available for the hosts where the Cloud Agent will be deployed to ensure accurate deployment. Ensure that the provided authentication credentials are correct.
- The target host should be up during the scan.
- The Unix target host should have the SSH service running during the scan.
- The Windows target host should have SMB service and Windows Remote Management service running during the deployment.
Benefits
- Significantly streamlines the Cloud Agent installation process.
- Reduces deployment time and effort as there is no need to rely on third-party tools to install Cloud Agents.
- Enhances operational capabilities by simplifying the Cloud Agent deployment workflow that is integrated with Qualys Cloud Platform.
- Secured deployment by allowing to configure Cloud Agent to use a proxy server for communication with Qualys Cloud Platform.
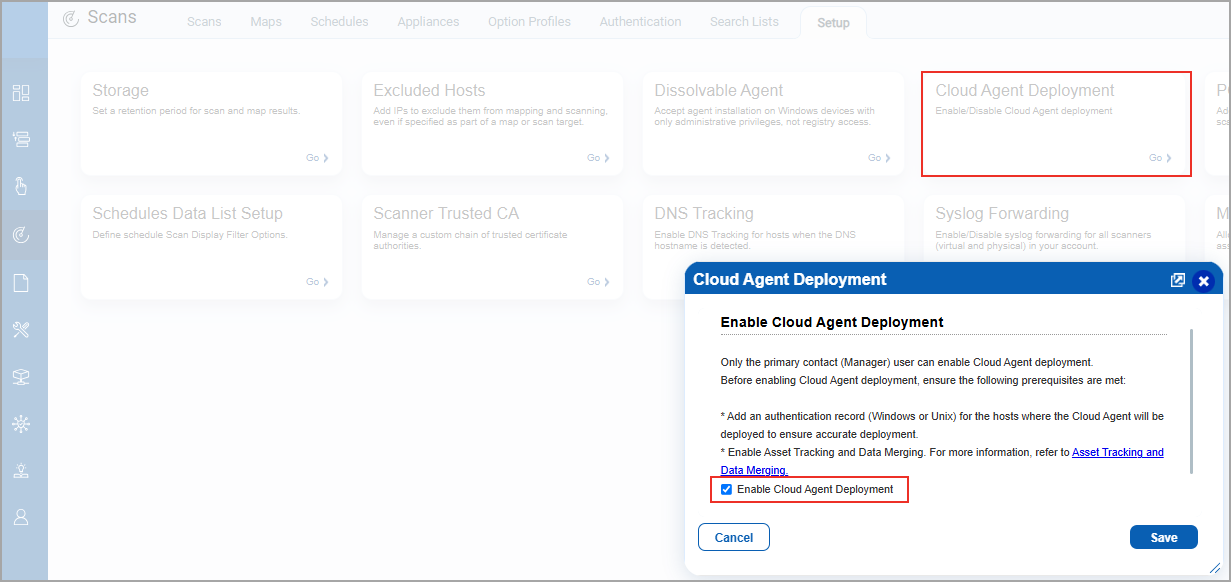
To enable this feature, navigate to the Scans > Setup > Cloud Agent Deployment tab and select Enable Cloud Agent Deployment.
This reduces the deployment time and effort and also enhances the operational capabilities by securing the deployment process.
This feature is available only for VMSP enabled subscriptions.
If you want to disable this feature, contact Qualys Support or your Qualys TAM.
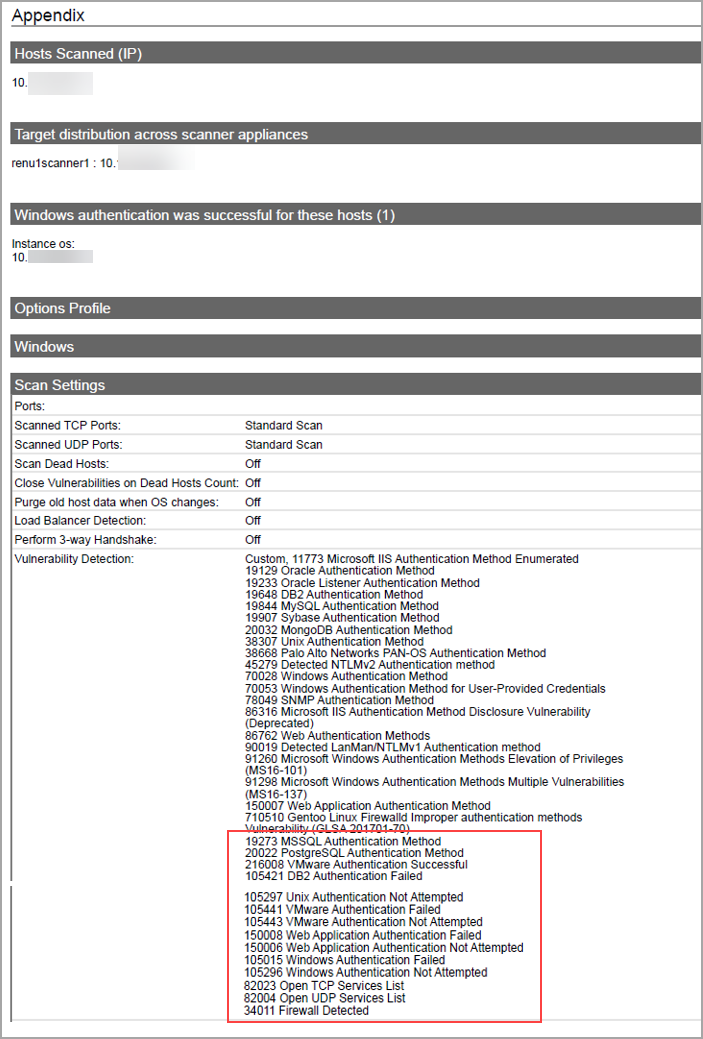
Added Additional QIDs in the Scan Result Report
With this release, you can now view the following list of new additional QIDs in the scan result report:
- Authentication Failure
- Authentication Not Attempted
- Open TCP Services List
- Open UDP Services List
- Firewall Detected
These QIDs are displayed when you perform a scan on any assets or IPs by enabling the Enable authentication testing checkbox(Scans > Option Profiles > New > Option Profile > Scan > Test Authentication).
Earlier only QIDs with Authentication Method and Authentication Successful were displayed in the report. To display the QIDs related to failure and not attempted, you had to perform a complete scan or create another search list by including the remaining authentication-related QIDs and run the scan again. With this enhancement, you can identify and resolve critical issues, ensuring more accurate and complete vulnerability scan.
Notification to Assess Readiness for PCI DSS 4.0
With this release, we have introduced support for Payment Card Industry Data Security Standard (PCI DSS) 4.0, the latest version designed to address evolving security threats and technological advancements. This updated standard focuses on continuous monitoring and allowing organizations to tailor security strategies based on unique risks and business priorities. These compliance requirements can be met using Qualys File Integrity Monitoring (FIM) and TotalAppSec.
For more details, refer to PCI Compliance Solutions and Qualys PCI DSS 4.0 Compliance Whitepaper.
Additionally, we have added a pop-up message highlighting the requirement for FIM and TotalAppSec, which ensures that help maintain compliance with PCI DSS 4.0 standards.
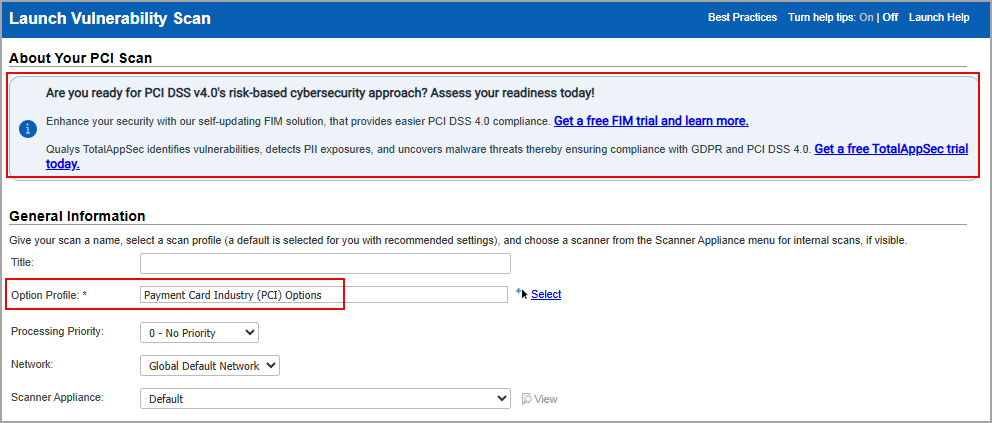
When performing a new vulnerability scan (Scans > New > Scans) for the Option Profile, we select Payment Card Industry (PCI) Options. This displays the pop-up messages, reinforcing this requirement.
The the pop-up messages include the following two links:
The pop-up message appears only if your subscription does not include access to the FIM and TotalAppSec modules.
Support for PCI DSS 4.0
With this release, we have introduced support for Payment Card Industry Data Security Standard (PCI DSS) 4.0—the latest version of the series, which focuses on evolving security threats and technology. This updated standard emphasizes continuous monitoring and enables organizations to prioritize security strategies based on unique risks and business priorities. Under PCI DSS 4.0, organizations are encouraged to adopt a risk-based approach to cybersecurity implementation. By leveraging robust threat intelligence, organizations can better understand and prioritize their risks, ensuring efficient resource allocation and faster resolution of critical issues.
PCI DSS 4.0 has updated scanners that enforce stricter rules for payment page scripts, primarily focusing on third-party scripts while providing less emphasis on non-critical scripts such as analytics. Additionally, web application scanning now includes payment-related applications, APIs, and dependencies. While continuous monitoring is encouraged, quarterly Approved Scanning Vendor (ASV) scans remain mandatory.
Qualys Vulnerability Management, Detection, and Response (VMDR) aligns with PCI DSS 4.0 updated standards, enhancing vulnerability detection and response while ensuring continuous compliance. Authenticated scanning is a new PCI DSS 4.0 requirement. Unlike other scanners, VMDR performs authenticated scans, including certificate inventory. It includes Qualys PCI ASV Compliance, ensuring compliance for external scans as required by PCI DSS 4.0. As an ASV, Qualys is authorized by the PCI Security Standards Council to conduct the quarterly scans necessary for demonstrating PCI DSS compliance.
For more details, refer to PCI Compliance Solutions and Qualys PCI DSS 4.0 Compliance Whitepaper.
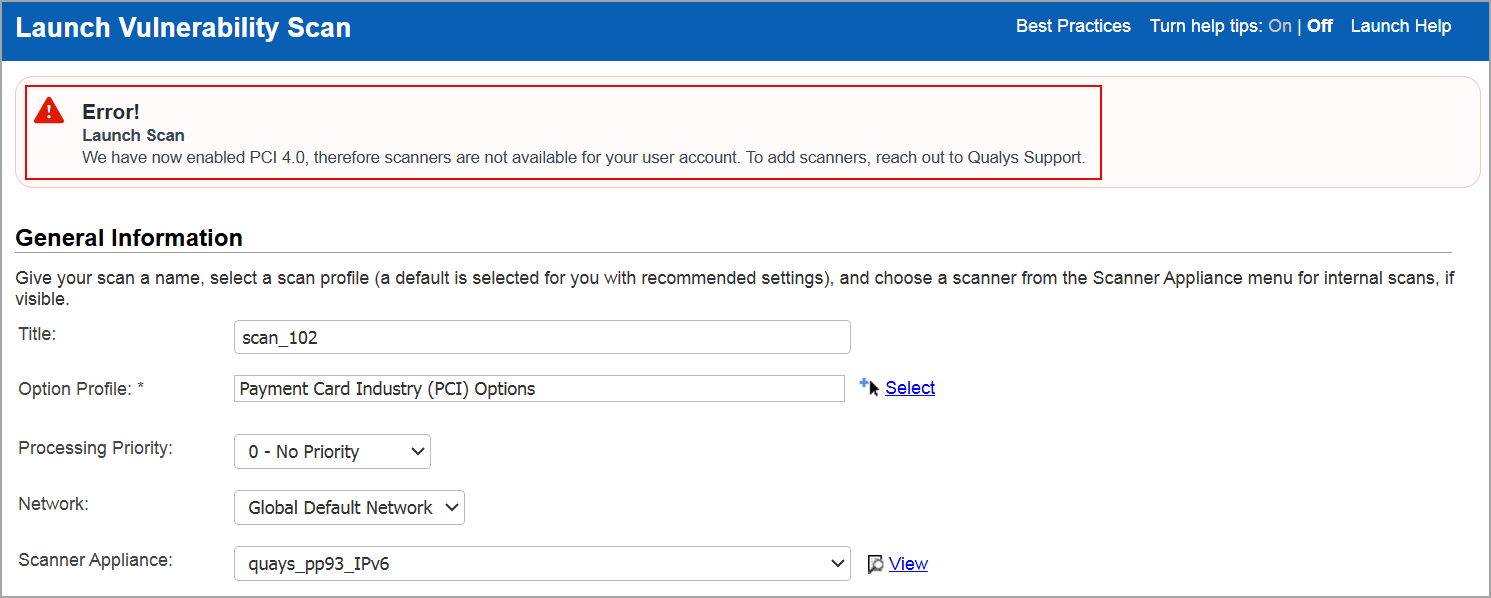
By introducing PCI DSS 4.0, we are improving the performance of PCI scans by introducing new scanner capabilities. Qualys Enterprise TruRisk Platform, being an ASV, performs scans explicitly targeting systems handling card data (authorization, storage, or processing). PCI DSS 4.0 support is available only for external scanners and does not extend to internal scans. Non-PCI systems such as marketing sites are excluded from scans unless they have an impact on payment security.
To comply with PCI DSS 4.0, it is mandatory to have advanced scanners configured on your system.
To enable PCI DSS - 4.0 for your subscription, contact Qualys support.
If your subscription is not configured to support PCI 4.0, the following error message is displayed:
Contact Number now Optional when Creating/Updating User Account
With this release, we have made an enhancement to make the phone number optional in the following scenarios:
- When a new subscription is created/edited and during the process of onboarding.
- When you add/edit any sub-user by navigating to Users > New/Edit.
- When you edit the user profile for the Manager and Non-Manager accounts.
Earlier, providing the contact number was mandatory, which is now optional. This allows you to sign up faster while safeguarding your security.
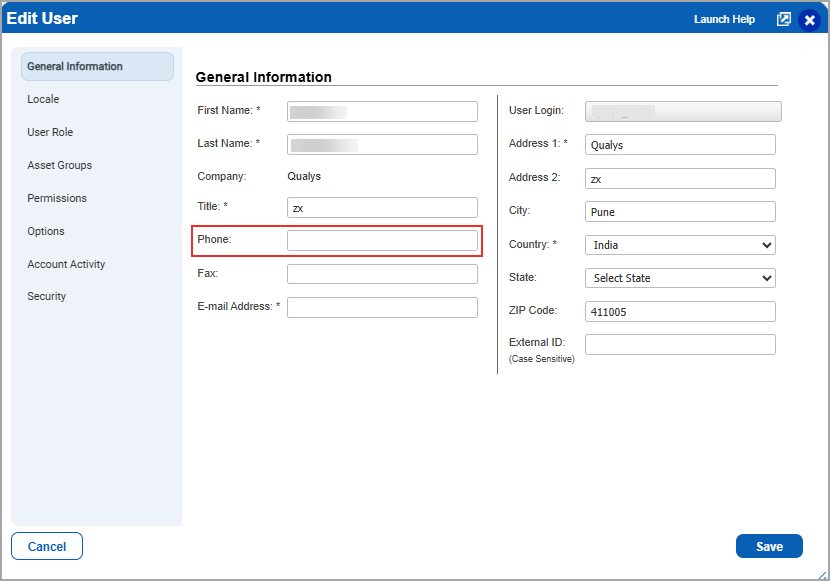
Contact number is optional for both new and existing users.
Qualys API Support for Making Contact Number Optional
For this enhancement, we have updated an input parameter in the /msp/user.php/ API. For more information, refer to Enterprise TruRisk platform 10.33 API Release Notes.
Qualys Policy Compliance (PC)
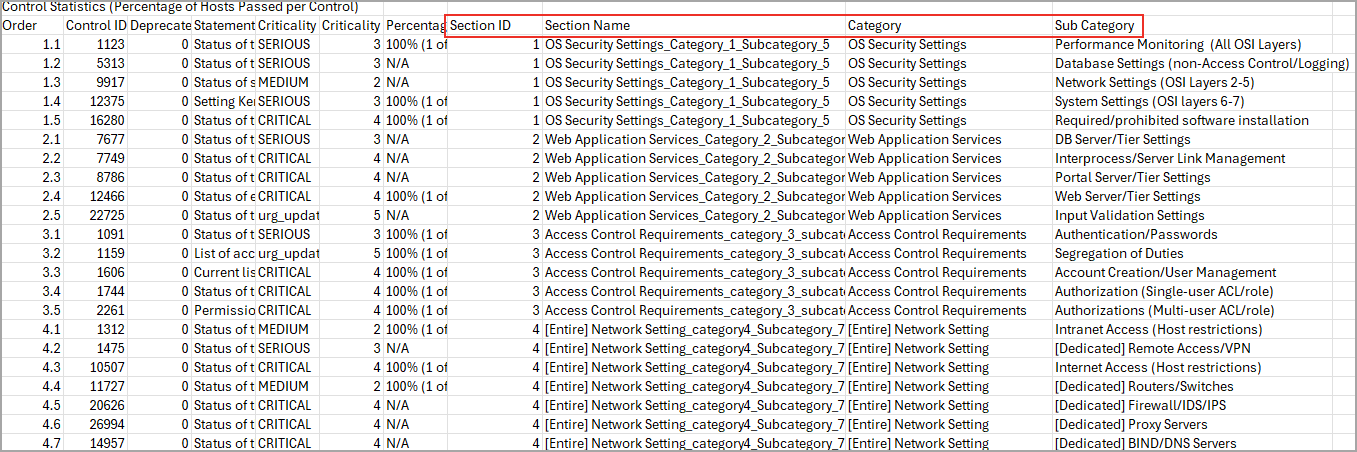
Enhancement in the Policy Compliance Report Template
With this release, you can include control statistics information in the Policy Compliance report in the CSV format.
With this enhancement, you can now identify the control categories and their subcategories and section id and section name of the control from the policy. This additional information helps you to easily locate the controls from the policies.
To include control statistics in the report:
- Navigate to Reports > Templates tab.
- In the Templates tab, click New> Policy Template > Layout tab
- Under Report layout > Select Group By - Host/Control/Control Reference from the list.
- Under Report section > Control Statistics > Select the following checkboxes:
- Section Details for CSV Reports Only: This includes Section ID and Section Name.
- Category details for CSV Reports Only: This includes Category and Sub Category.
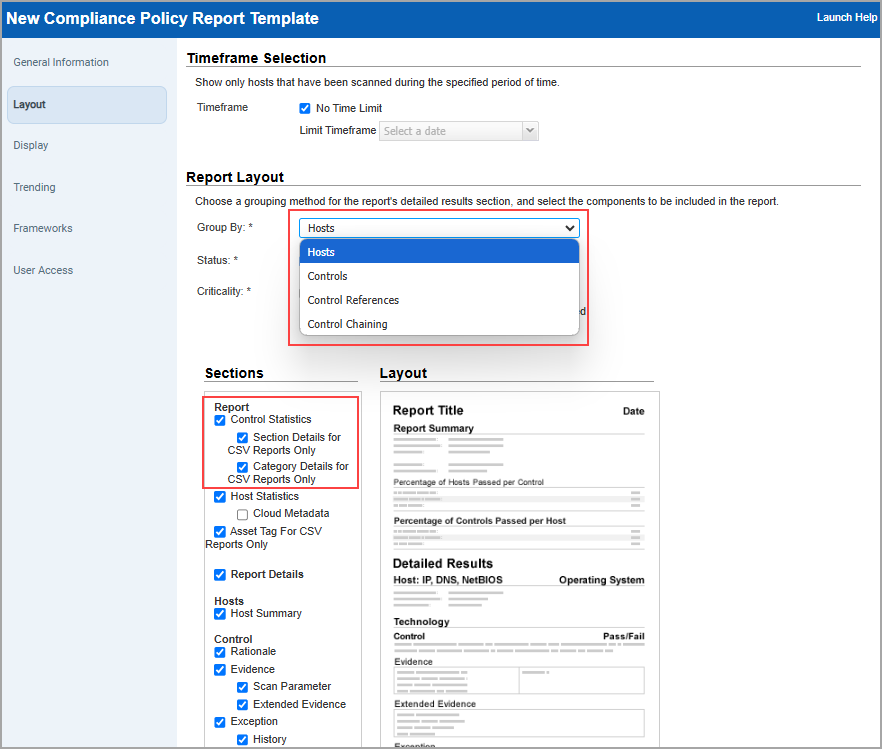
Group By Control Chaining report is not impacted.
On selecting both checkboxes, the report displays the section and category details in the CSV policy report.
These options are disabled by default. When you create a new template, ensure to enable the Control statistics checkbox and then enable the above checkboxes.
If you have an existing Compliance Policy Report, template, edit the existing template, select the checkboxes, and save the changes.
Support for New Technologies
With this release, the following technologies are now supported for Policy Compliance scans:
VMware Tomcat Server
With this release, we have added support for VMware Tomcat Server 4.x and 5.x for Scanner using Tomcat Server authentication records (PC > Scans > Authentication > New > Applications > Tomcat Server).
The technology is now available for use at the following places for Scanner:
Policy Editor
When you create or edit a compliance policy, VMware tc Server 4.x and 5.x are now available in the list of supported technologies.
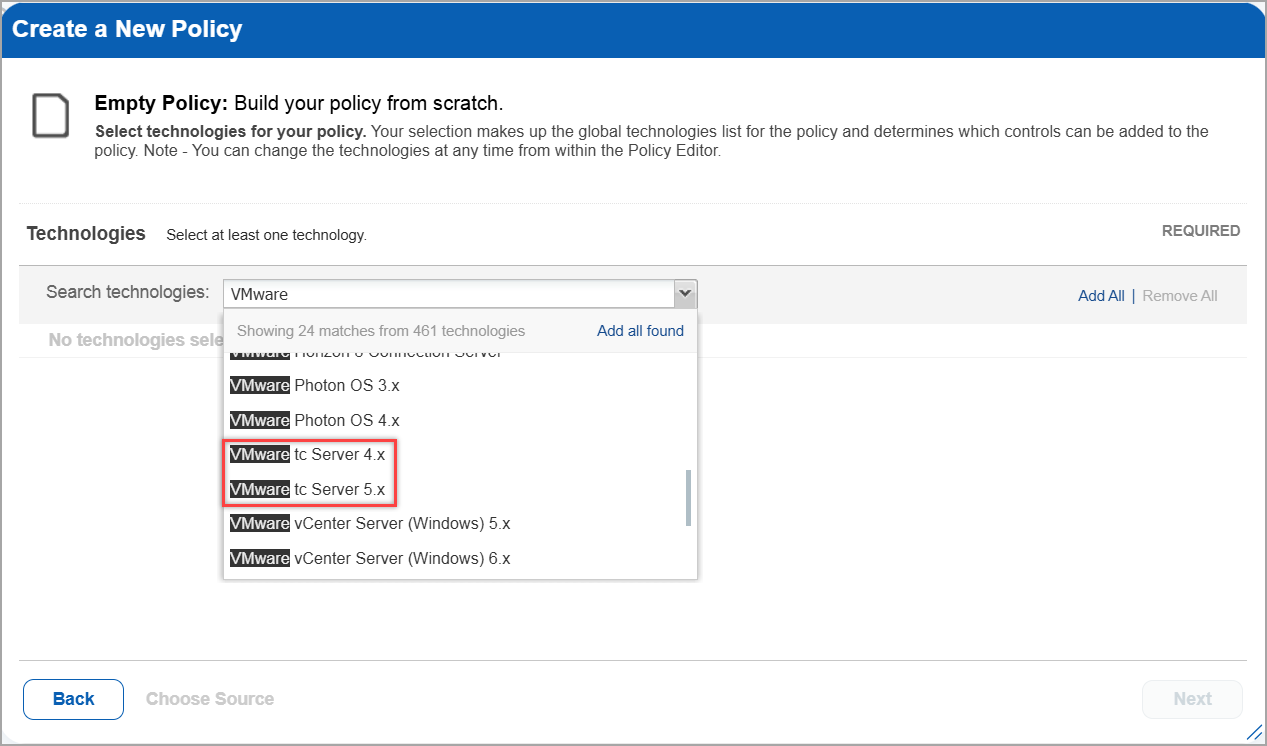
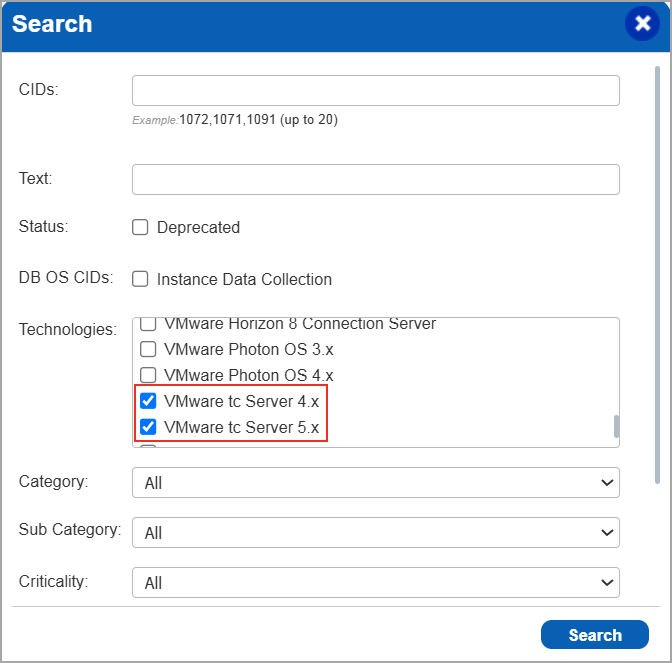
Search Controls
When you search controls, you see VMware tc Server 4.x and 5.x in the list of technologies. Go to Policies > Controls > Search and select VMware tc Server 4.x or 5.x in the list.
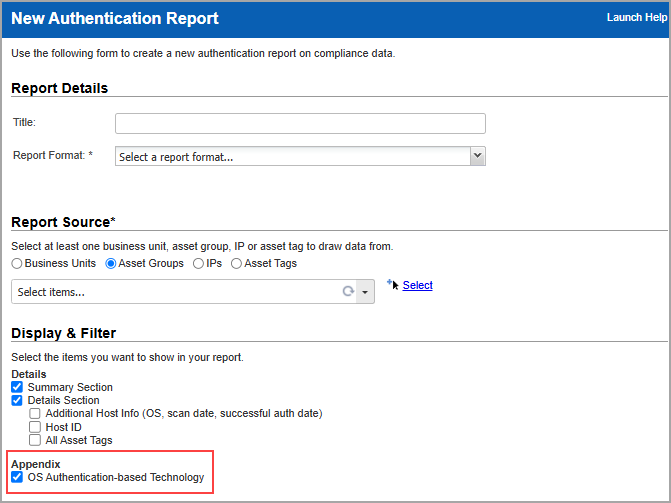
Authentication Report
To display all OS authentication-based instance technologies per host, including VMware tc Server, in your authentication report, go to Reports > New > Authentication Report and under Appendix, enable OS Authentication-based Technology option.
VMware tc Server is now listed under application technologies in the Result section of a compliance scan report.
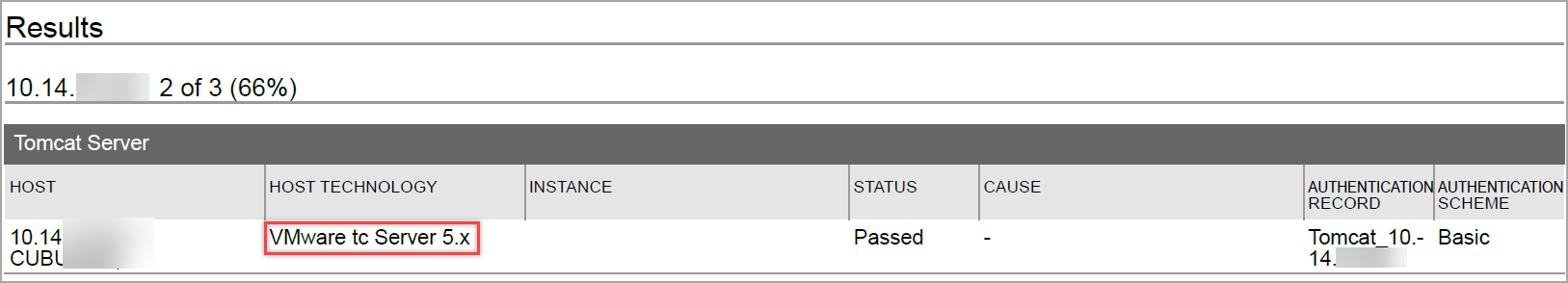
Compliance Result
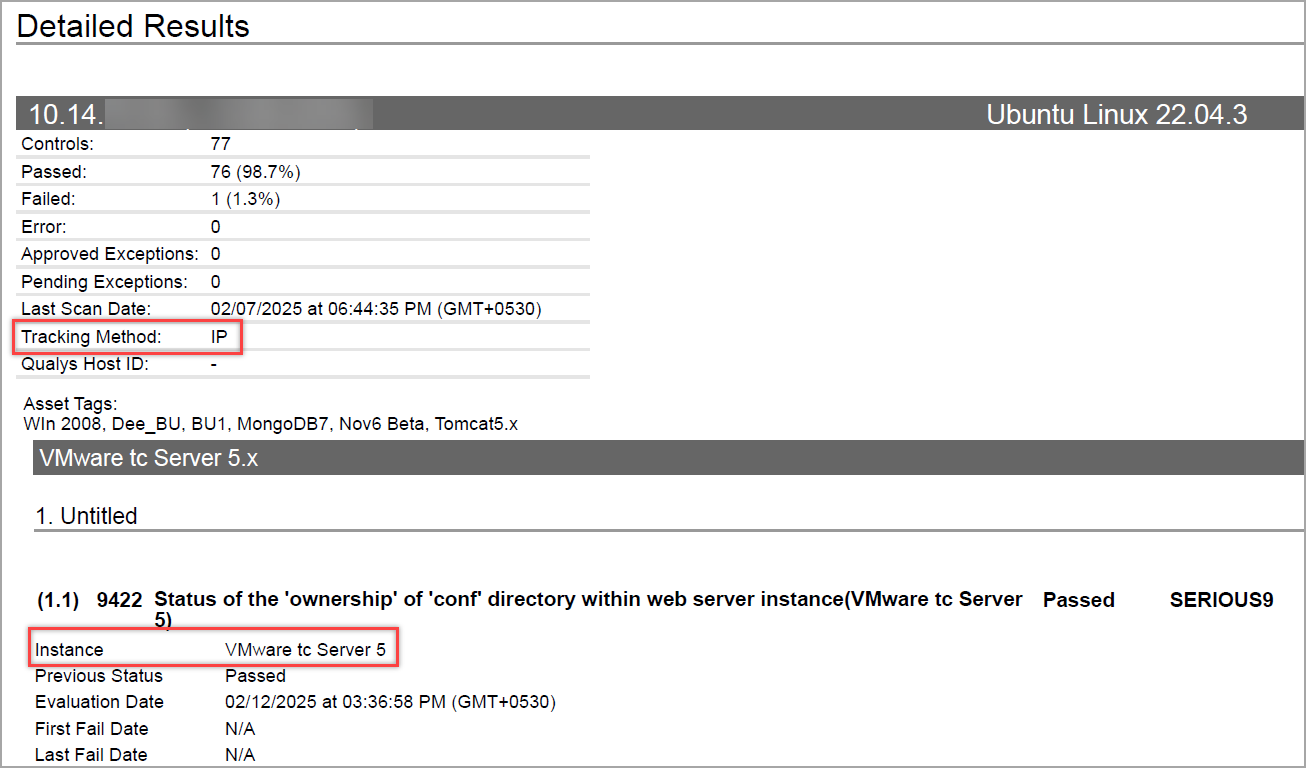
The compliance report displays the sample report for scanner.. You can view the instances of VMware tc Server for scanned hosts in compliance reports.
The compliance report displays the tracking method and the instances for the scanner. You can view the instances of VMware tc Server for scanned hosts in compliance reports.
For more information, see Authentication Technologies Matrix.
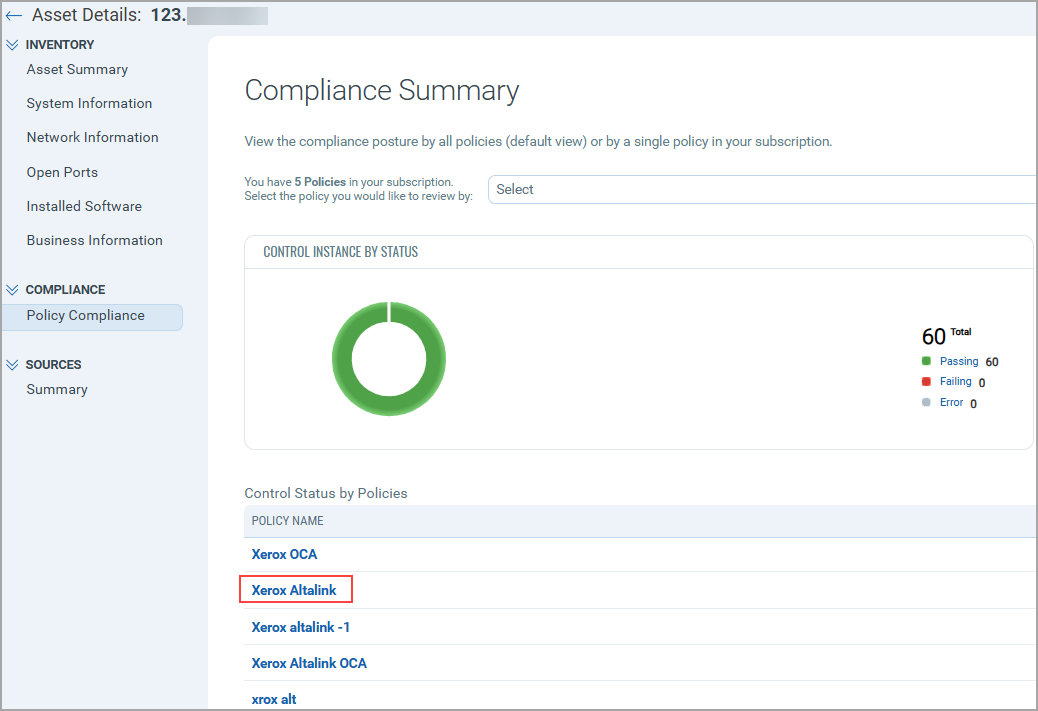
Xerox AltaLink
With this release, we have added support for Xerox AltaLink in the Out-of-Band Configuration Assessment (OCA) Compliance. This technology helps you to process the OCA assets data using Policy Compliance.
The technology is now available for use at the following places:
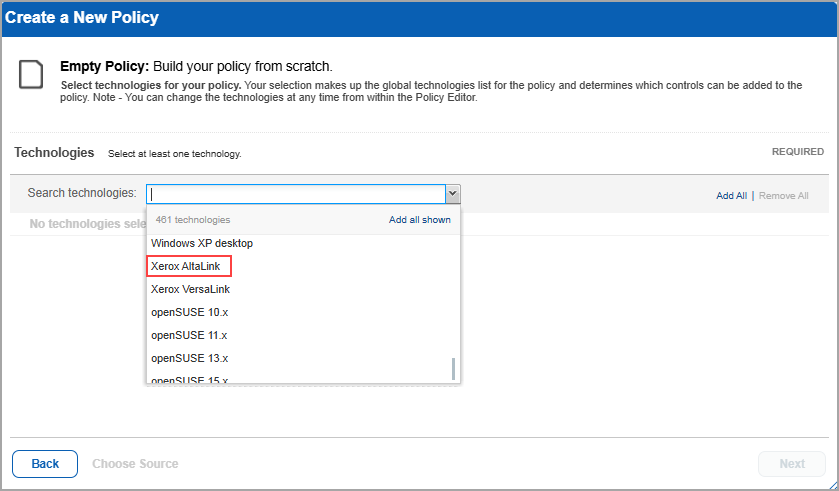
Policy Editor
When you create or edit a compliance policy, Xerox AltaLink is now available in the list of supported technologies.
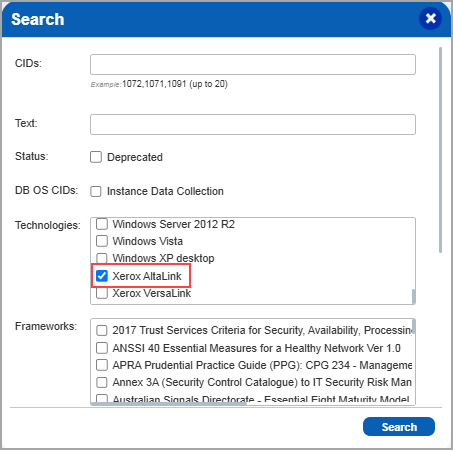
Search Controls
When you search controls, you can see Xerox AltaLink in the list of technologies. Go to Policies > Controls > Search and select Xerox AltaLink in the list.
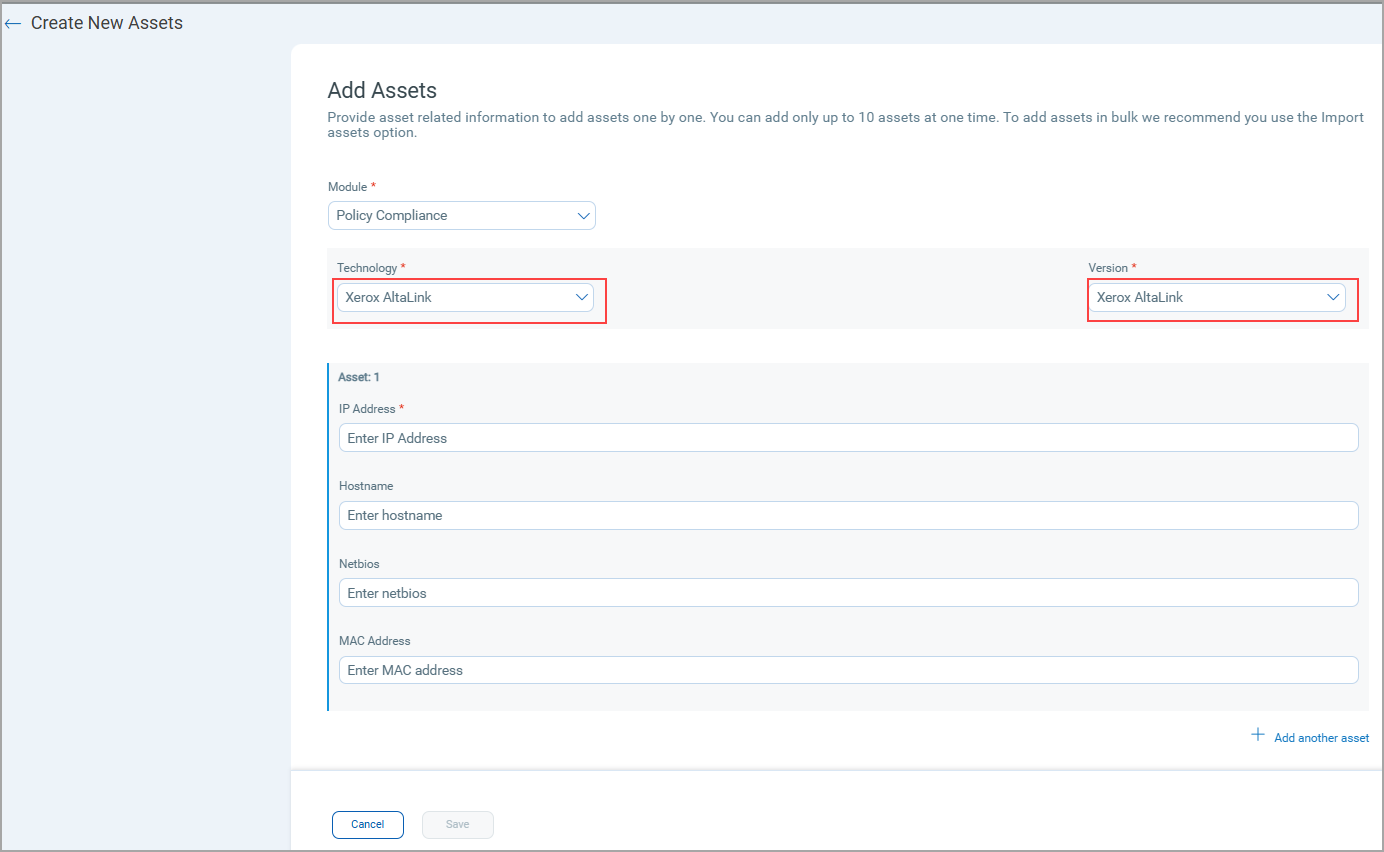
Out-of-Band Configuration Assessment (OCA)
When you create new Assets in OCA ( OCA > Assets > Add Assets > New), Xerox AltaLink is now available in the list of supported technologies under the Policy Compliance Module.
You can view the list of assets created using Xerox AltaLink.
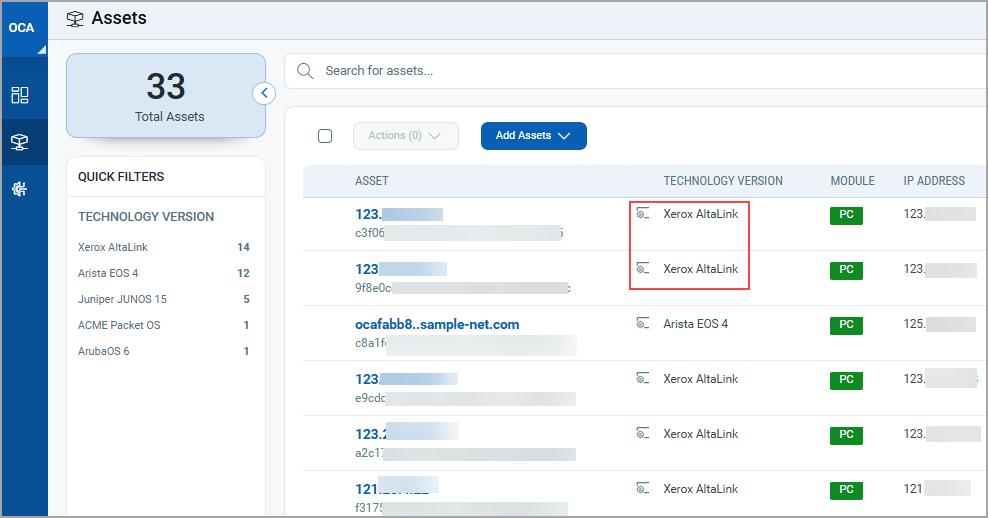
You can view the compliance summary of an asset when you select View Details from the list under Quick Actions.
New UDC Technology Support for Azure Microsoft SQL Server 2014
In this release, we have added new User Defined Control (UDC) technology support for Azure Microsoft SQL Server 2014. You can now create a new UDC where you can select and use Azure Microsoft SQL Server 2014 under Control Technologies.
Perform the following steps to create a new User Defined Control (UDC) for Azure Microsoft SQL Server 2014 using new control technology support:
- Navigate to Policies > Controls. Here we provide many controls for you to choose from and create your own UDCs.
- Click New > Control.
The New Control window is displayed. - In the left pane, select Database Control Types.
- Select MS SQL Database Check control type from Database Control Types list.
- Under Control Technologies, select Azure Microsoft SQL Server 2014 from the list and provide the mandatory information.
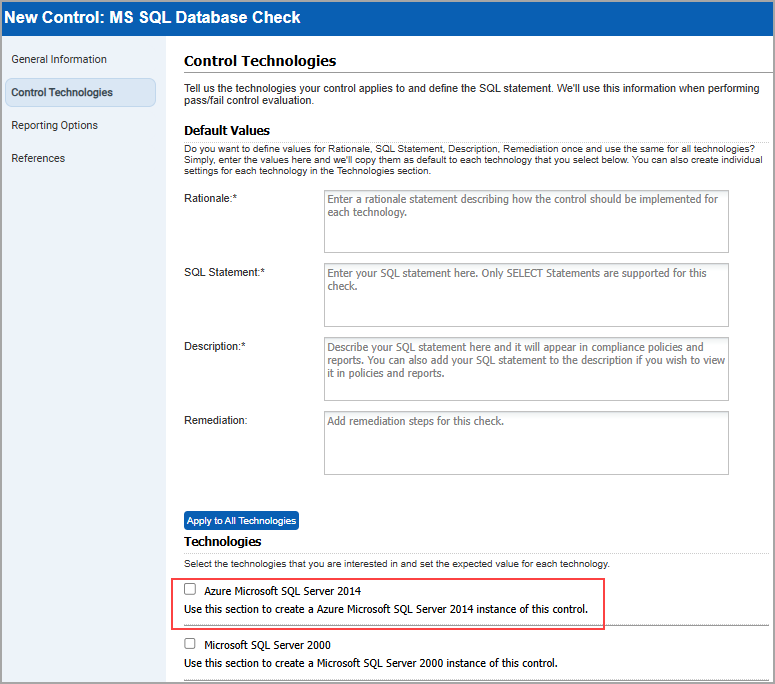
- Click Create.
The new UDC with support for Azure Microsoft SQL Server 2014 is created.
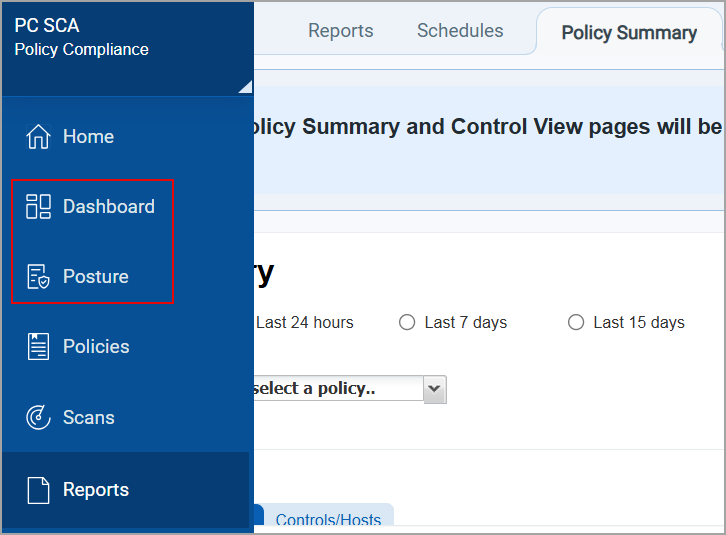
Policy Summary and Control View Deprecation Notification
With this release, we have added a notification informing users that the Policy Summary and Control View pages will be deprecated on August 1, 2025.
To navigate to the notification, goto Reports > Policy Summary.
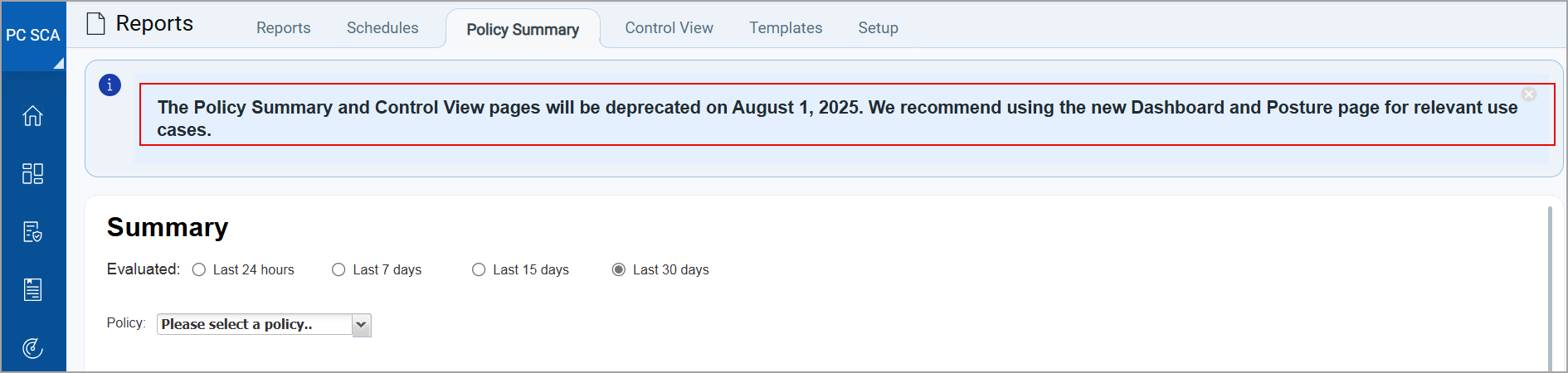
The details previously available on these pages can now be accessed through the Dashboard and Posture tabs.
User Interface (UI 4.0) of the Qualys Enterprise TruRisk™ Platform
Our goal is to continuously improve user interaction with the Qualys Enterprise TruRisk™ Platform through UI enhancements. With this release, we have made the following changes:
- UI 4.0 implementation - We have now implemented the new UI at the following locations in the Qualys Enterprise TruRisk™ Platform, where it was previously unavailable:
- Navigation and Controls - Updated Actions, New, Filter, and Pagination Navigation across all tabs.
- Information Messages - Improved display and clarity for messages on all tabs.
- Updated UI in the following tabs:
- VM/VMDR > Assets > Applications
- VM/VMDR > Assets > Ports/Services
- VM/VMDR > Reports > Risk Analysis
- VM/VMDR > Assets > Asset Search
- PC > Reports > Policy Summary
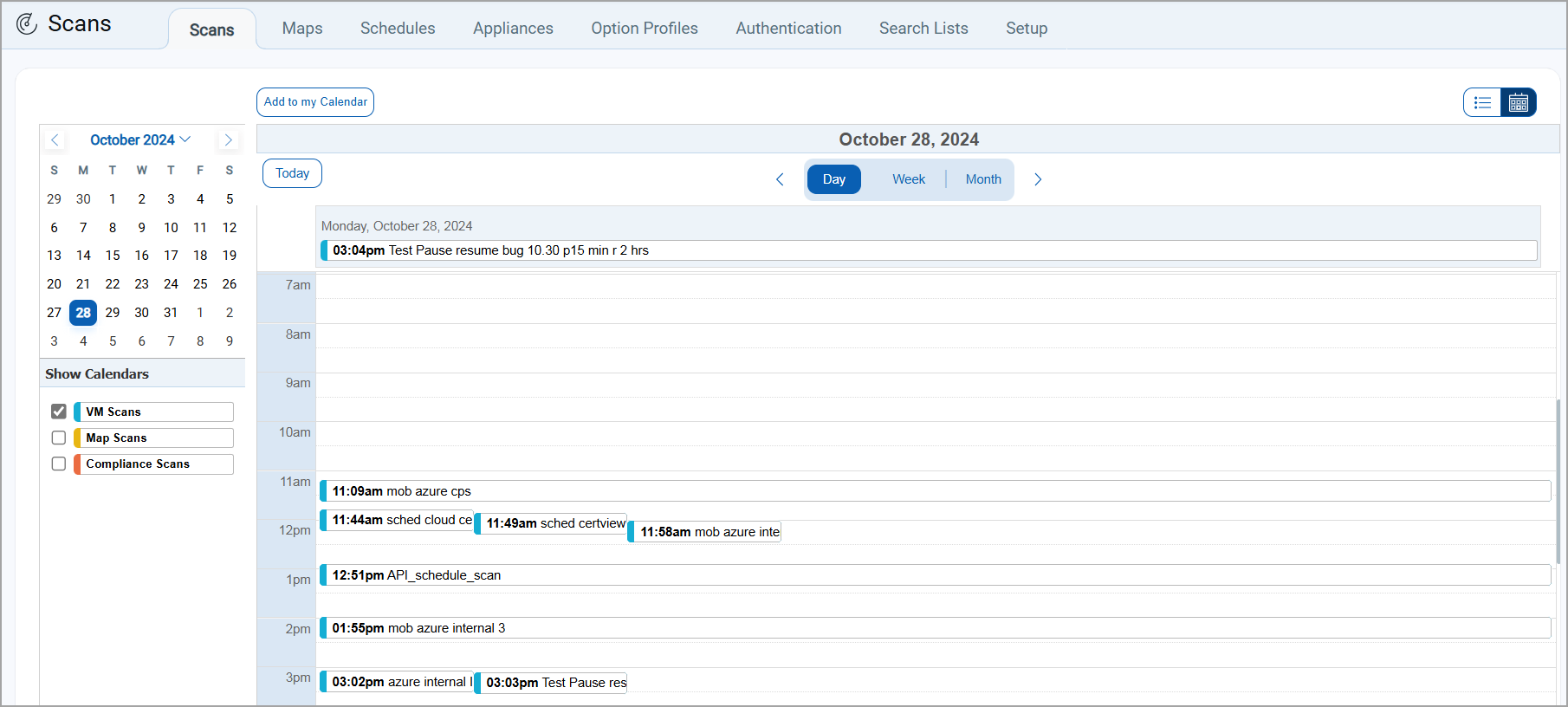
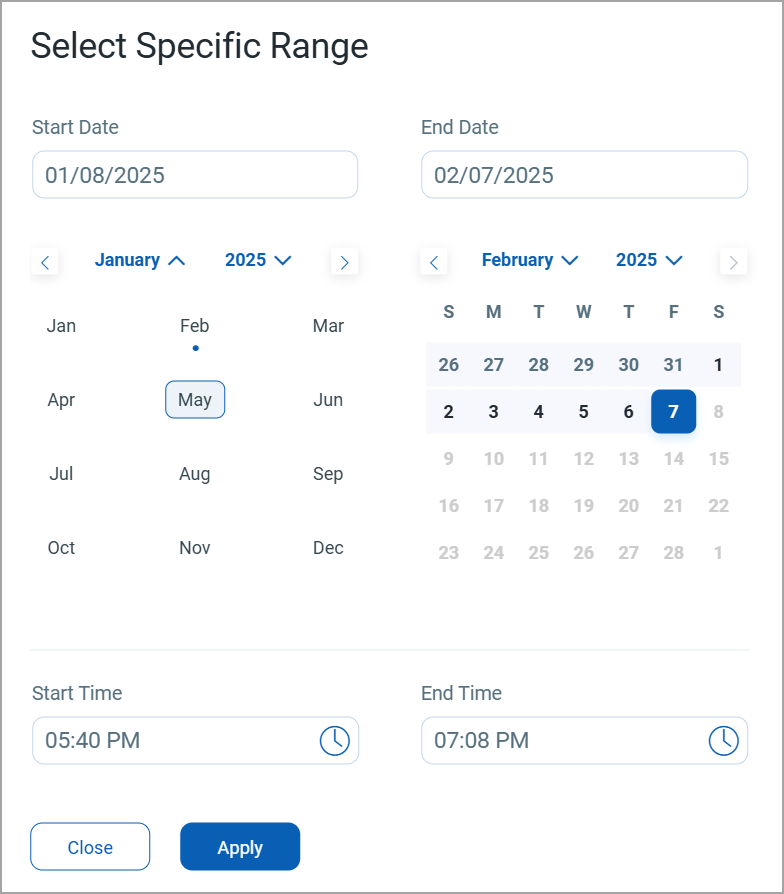
- Calendar Enhancements - We have updated the Calendar view across all tabs, offering a smoother and faster experience. The refreshed design features a light theme for a modern and visually appealing look.
- Calender view for Day, Week, and Month
- Updated calendar icon with a new month/year selection menu
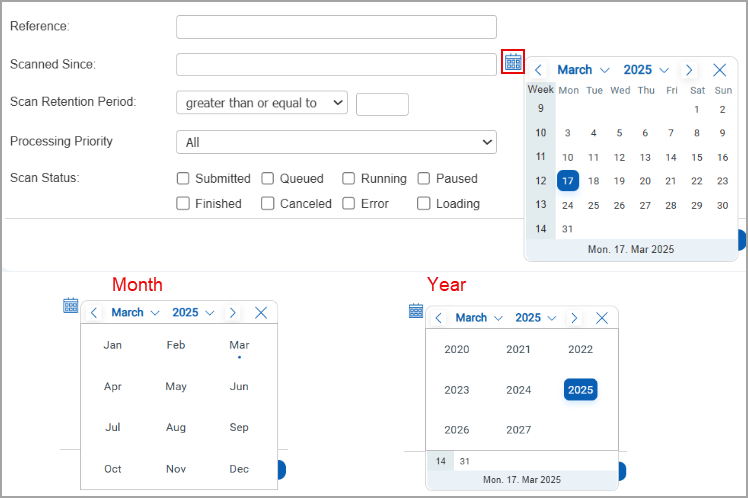
- Updated date range selection
- Calender view for Day, Week, and Month
Issues Addressed
The following reported and notable customer issues are fixed in this release:
| Component/Category | Application |
Description |
| VM - Scan Based Report | Vulnerability Management | When the users launched a scan and generated a scan result report, the report was interrupted, and were unable to download the report in PDF format. Relevant code changes have been made to fix the issue. |
| VM - User Management | Vulnerability Management | When the users configured VMDR user password expiry, no email notifications were received regarding the password expiry. Relevant code changes have been made to fix the issue. |
| Licensing - Addon Enable/Disable | Vulnerability Management | When the users tried to grant permissions to two sub-users for the Web Application module without adding the VM or PC module, an issue was observed. One of the sub-users encountered errors, which was expected as per the design. However, the other sub-user was able to save the configuration, which was not as per the intended design. Relevant code changes have been made to fix the issue. |
| VM - User Management | Vulnerability Management | When the users tried to create a PCI merchant account with an email address with a different format, the system did not accept the mentioned email address and displayed an error message. Relevant code changes have been made to fix the issue. |
| VM - Asset API | Vulnerability Management | When the users used the API script to add the scanner appliance to the asset group using the scanner ID parameter, the scanner appliance was not getting updated in the asset group list. Relevant code changes have been made to fix the issue. |
| VM - Host List Detection API | Vulnerability Management | When user executed HLD API by including the input parameter Exclude Supersede QIDs on multiple hosts, incorrect QIDS were getting excluded from API result. Relevant code changes have been made to fix the issue. |
| Documentation | Vulnerability Management | When the users tried to create a scheduled map scan using the API /msp/scheduled_scans.php?, they were unable to find the details in the latest API User Guide. Now we have updated the API User guide with relevant information. For details Refer to Qualys API (VM/PC) Guide. |
| VM - Scan Schedule | Vulnerability Management | When the users scheduled a scan and later changed only its title, they observed that the scan ran at a different time instead of the scheduled timing. Relevant code changes have been made to fix the issue. |
| VM - Host List Detection API | Vulnerability Management | When the users were calling the 'vm_processed_before' parameter in the Host List Detection (v2.0 and v3.0) and the Host List (v2.0, v3.0, and v4.0) APIs , they were not receiving the expected results. Relevant code changes have been made to fix the issue. The issue persisted because of the way the query handled date conditions. We have now documented this behavior in the Host List Detection and the Host List APIs section in the Qualys API (VM/PC) User Guide. |
| PC | Policy Compliance | When the users created or edited an Oracle Authentication record and saved the changes, they encountered an error stating that the maximum length for a field is 10000 characters. However, the error message did not specify which field exceeded the limit. Relevant code changes have been made to fix the issue. Now, the error message clearly identifies the affected fields, Cwallet and Ewallet, where the character limit is enforced. |
| PC - PCRS Reports | Policy Compliance | When users exported a Policy Compliance report in CSV format, they noticed that the # character used in the regular expression for a Control did not appear in the exported file. However, it was retained in the XML format. Relevant code changes have been made to fix the issue. |