Third-Party Asset Import in CSAM
You can identify the third-party assets scanned or discovered by various data connectors, such as Webhook, Active Directory, and ServiceNow, and import them to CyberSecurity Asset Management (CSAM) inventory. As a result, all third-party assets or data are merged with Qualys assets, or new unmanaged assets are created, and you get visibility on how assets are deduplicated.
Out-of-the-box Third-Party ConnectorsOut-of-the-box Third-Party Connectors
Having a reliable and comprehensive inventory of all your assets is essential to manage your IT assets effectively. Using the third-party data connectors, you can find your non-agent or Qualys non-scanner assets unavailable in Qualys and create unmanaged assets in Qualys.
You can then add them to your vulnerability management program. Qualys connectors enable continuous visibility and security across all your cloud environments. You can configure your connector and discover assets in your cloud account. Connectors integrations let you create connectors for third-party services, discover resources and pass the information to the required Qualys modules, such as CSAM.
- Webhook: The Webhook connector lets you connect and discover assets of third-party inventories. You can then view the discovered assets in the CSAM application. In the case of Webhook connectors, the CSAM APIs are required to establish a connection with any third-party service. you must send the API request to identify or discover the assets and bring them to the CSAM inventory. For more information, refer to the Import Third-Party Assets section from the API v2 User Guide.
- Active Directory: The Active Directory (AD) connector lets you fetch the assets data from your Azure AD server. The connector then passes this data to the CSAM application.
- ServiceNow: The ServiceNow Inventory connector lets you connect and discover resources of ServiceNow inventories. You can then view the discovered assets in the CSAM application.
- BMC Helix (Beta) Connector: The Qualys BMC Helix CMDB Connector automatically synchronizes comprehensive information about your global IT resources so that the Qualys Asset Inventory can be monitored continuously. The BMC Helix Connector leverages Qualys' highly distributed and scalable cloud platform and various data 'collection tools, including Qualys Cloud Agents, to compile and continually maintain a complete inventory of your IT assets. The connector offers two-way synchronization, allowing you to discover Qualys assets in your BMC Helix environment.
- VMWare ESXi Connector: The Qualys VMWare ESXi Connector automatically synchronizes comprehensive information about your vCenter VMs for Qualys Asset Inventory to monitor continuously. The VMWare ESXi Connector leverages Qualys' highly distributed and scalable cloud platform and various data 'collection tools, including Qualys Cloud Agents, to compile and continually maintain a complete inventory of your instances. The connector offers two-way synchronization, allowing you to discover Qualys assets in your VMWare ESXi Connector.
Important: VMware ESXi version 1.0.0 is a prerequisite for the functioning of the VMware ESXi connector for scanning assets from CSAM.
Third-party Asset Import Workflow
Third-party asset import is a collaborative effort of third-party data connectors and CSAM capabilities. The following is the end-to-end workflow for third-party asset import.
1. Asset Identification Rules Creation1. Asset Identification Rules Creation
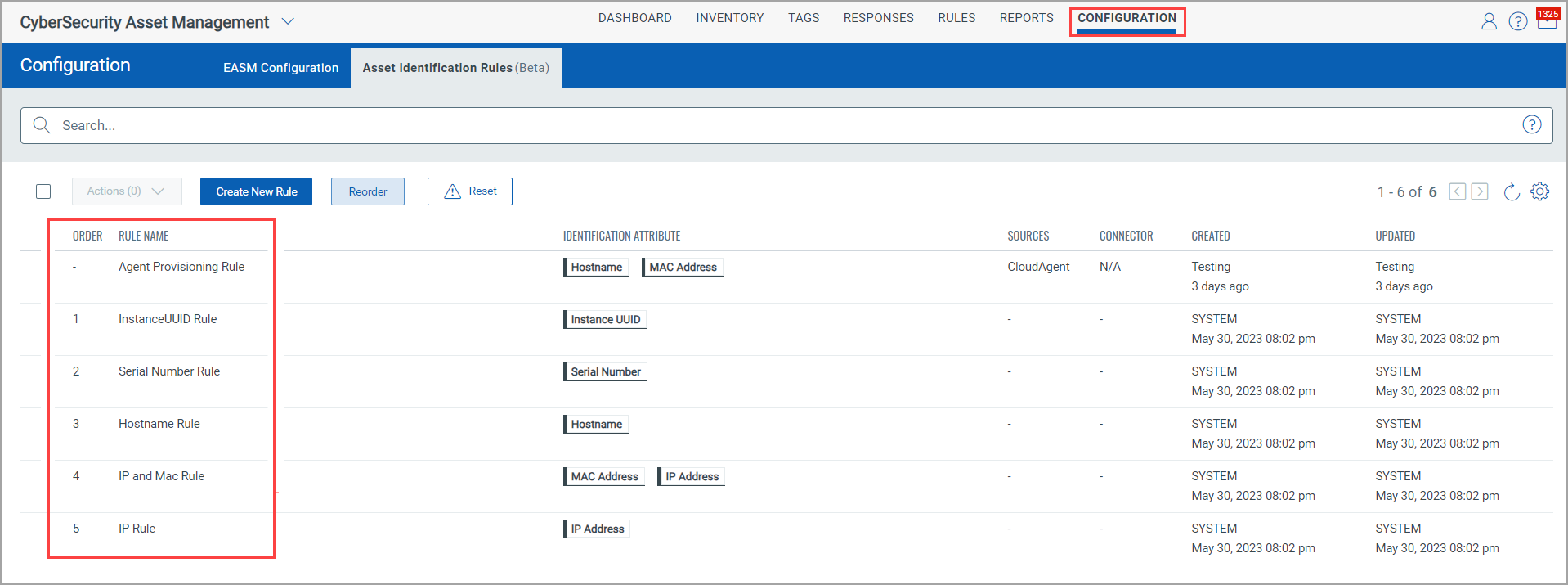
After the feature is activated, you can see the default asset identification rules and create the asset identification rules from the CSAM > Rules >Asset Identification > Rules.
You can see no details in the Order column for the Agent Provisioning Rule for Cloud Agents.
- You can see this rule only if it is enabled. Contact your Technical Account Manager (TAM) to view and use this rule.
- After enabling this rule, the Agent Provisioning Rule is created by default in CyberSecurity Asset Management (CSAM) and Global AssetView (GAV) applications.
2. Connectors Creation2. Connectors Creation
The Webhook, Active Directory, and ServiceNow connector sources are created from the Connectors application. You need to create the required connectors for the respective connector sources.
For more information, see Create Active Directory Connector, Create ServiceNow Connector, Create Webhook Connector, and Create VMWare ESXi Connector.
You can specify the Asset Identification Rule for the connector from the Connectors application.
The toggles next to the default or system-generated and user-created asset identification rules are turned ON by default. If you want to exclude specific Asset Identification Rules, you can do it by turning the toggles OFF.
To find detailed information about how the identification rules logic work, how the newly identified assets are merged into the existing assets, and the logic that explains how single-match and multi-match assets are found, refer to Identification Rule Selection.
4. Asset Identification4. Asset Identification
Based on the single-match and multi-match logic, asset identification is done by connectors. To know the details about these logics, see the "Identification Rules Logic for Asset Merge" section from the Identification Rule Selection topic.
For Webhook, the CSAM APIs are a must to establish a connection with any third-party service. Hence, in the case of Webhook connectors, you must send the API request to identify or discover the assets and bring them to the CSAM inventory.
5. Asset Import in CSAM Inventory5. Asset Import in CSAM Inventory
After the assets are discovered based on the asset identification rules selected for the respective connector, they are merged and imported into the CSAM inventory. For more information, refer to the "Third-Party Assets into CSAM Inventory" section from Creating Asset Identification Rules topic.
6. Reconciliation Rules Configuration6. Reconciliation Rules Configuration
The Reconciliation Rules) are essential when you want to merge assets that come from Qualys native sensors like Qualys agent or scanner when there are assets already identified by the third-party sources before they are discovered again through a different schedule.
Scenario: During asset sync or asset discovery, the same IP address may be discovered through different scans. For example, the IP and ServiceNow scan identifies two assets with the same IP address. One asset was found from a ServiceNow scan before the IP scan. If so, you can merge such assets into a managed asset by configuring and running the Reconciliation Rule.
7. Purge Rule Creation7. Purge Rule Creation
You can create purge rules to purge the third-party assets discovered by Webhook, ServiceNow, and Active Directory connectors.
If the asset type is a managed asset discovered by any third-party connector sources mentioned earlier, then only the third-party connector data is deleted; the asset is not purged.
If the asset is solely a third-party connector asset, which is an unmanaged asset, it gets purged if it satisfies the third-party connector purge rule. However, if multiple connector sources discover the same asset, only the respective connector data for which the purge rule is created gets purged. The asset gets deleted only when all the connector data for all the different connector sources gets deleted.
Good to Know!
You can reorder the default and the asset identification rules you created.