External Attack Surface Management (EASM)
Qualys CyberSecurity Asset Management (CSAM) provides comprehensive visibility through External Attack Surface Management (EASM). It provides an outside-in view of your external-facing IT infrastructure to continuously monitor your organization's external attack surface and internet-connected assets, track changes, and notify you when new or unknown assets or critical issues are found.
EASM is available as part of the Qualys CyberSecurity Asset Management (CSAM) module.
EASM provides you with a complete view of internet-exposed assets, along with numerous data points regarding attribution to your organization and subsidiaries, domains and subdomains, DNS misconfigurations, hosting providers, asset types, certificates, exposed ports and services, and vulnerabilities - all important cybersecurity risk factors that hackers are looking at to identify weaknesses to exploit.
Offering multiple ways to query and monitor external facing assets with interactive dashboards, inventory views, email alerts and reports, Qualys CSAM with EASM provides complete attack surface management functionality with business context, using first-class native integrations to other Qualys Cloud Platform modules like VMDR, CertView, Policy Compliance and WAS to help you improve your organization's risk posture, providing better outside-in visibility, more safety and cybersecurity, better compliance with industry regulations, better customer service, and more efficient operations.
Difference between EASM and CSAM
EASM provides an outside-in view by identifying internet-facing assets, uncovering domains, cloud services, and exposed interfaces that attackers can easily discover but that organizations often overlook.
CSAM provides the inside-out perspective by aggregating data from existing security and IT systems to build a unified inventory of all internal devices, workloads, identities, and applications within the organization's security boundary.
EASM focuses on internet-facing exposure, and CSAM provides clarity into internal assets. Together, they deliver a complete and accurate view of the organization’s attack surface, ensuring every asset is identified, validated, and secured.
How does EASM helps?
EASM helps you:
- Discover unknown internet-facing assets
- Identify exposed ports, services, software, and certificates
- Detect DNS misconfigurations and risky domains
- Assess whether discovered assets belong to your organization
- Prioritize external risk using TruRisk scores
- Bring unmanaged assets under Qualys management
Key Features of External Attack Surface Management
| EASM Feature | What It Does | Benefit |
|---|---|---|
| External Asset Discovery | Discovers domains, subdomains, cloud workloads, web applications, APIs, certificates, and services exposed to the public internet | Eliminates visibility gaps and reveals assets that exist outside formal IT processes |
| Asset Attribution and Mapping | Identifies which discovered assets belong to your organization and maps their relationships | Provides an accurate view of the external footprint and reduces uncertainty in asset ownership |
| Shadow IT and Cloud Sprawl Detection | Detects unapproved cloud services, test environments, and abandoned or forgotten assets | Helps regain control of unmanaged resources and reduces unintended external exposure |
| Certificate and Service Monitoring | Monitors certificates and exposed services for ownership, expiration, and changes | Prevents outages, misconfigurations, and risk caused by expired or mismanaged certificates |
| Continuous Change Detection | Detects newly exposed assets and changes to existing internet-facing services | Ensures new exposure is identified and tracked before it can be exploited |
| Integration with Security Workflows | Automatically adds discovered assets to CSAM and VMDR for assessment | Ensures all assets, including previously unknown ones, are evaluated using standard security controls |
| Risk Context Enrichment | Combines external exposure with ownership, business context, and risk scoring | Enables teams to prioritize remediation based on actual risk rather than raw asset counts |
How does EASM Work?
External Attack Surface Management begins by discovering external assets, assessing their risk, and prioritizing the remediation.
1. Asset Discovery and Mapping
External Attack Surface Management starts by discovering what is visible about your organization from the internet. EASM identifies internet-facing assets, such as domains, subdomains, cloud workloads, web applications, APIs, and services that expose public IP addresses.
Using external signals like DNS records, SSL/TLS certificates, hosting data, and cloud fingerprints, EASM continuously discovers assets that may not exist in internal inventories. These assets may be created by different teams, deployed in cloud environments, or exposed unintentionally.
Once discovered, EASM maps these external assets back to your organization and connects them to the internal asset inventory in CSAM. This mapping helps validate ownership, identify unmanaged assets, and create a complete outside-in view of the attack surface.
EASM discovery also identifies your leased IPv4 Netblocks and discovers assets exposed on those IPs using Shodan data. During the discovery process, the system retrieves IPv4 Netblocks linked to your organization or domain. The system then validates these IPs against Shodan data to enumerate them for discovering exposed assets.
To enable the discovery of assets on your leased IPv4 Netblocks, contact your Technical Account Manager (TAM).
2. Vulnerability Assessment and Risk Analysis
After discovery, assets are added to inventory and can be scanned using VMDR to assess vulnerabilities, exposed services, certificates, and configuration weaknesses.
This ensures that previously unknown or unmanaged assets receive the same level of security assessment as known assets.
3. Risk Prioritization and Remediation
The assessed assets are evaluated using the TruRisk™ algorithm, which evaluates and prioritizes vulnerabilities, misconfigurations, asset criticality, and external exposures based on their risk to the organization.
The remediation can then be performed by patching vulnerabilities, fixing misconfigurations, closing exposed ports, renewing certificates, or decommissioning unused assets.
Get Started with EASM
Access EASM
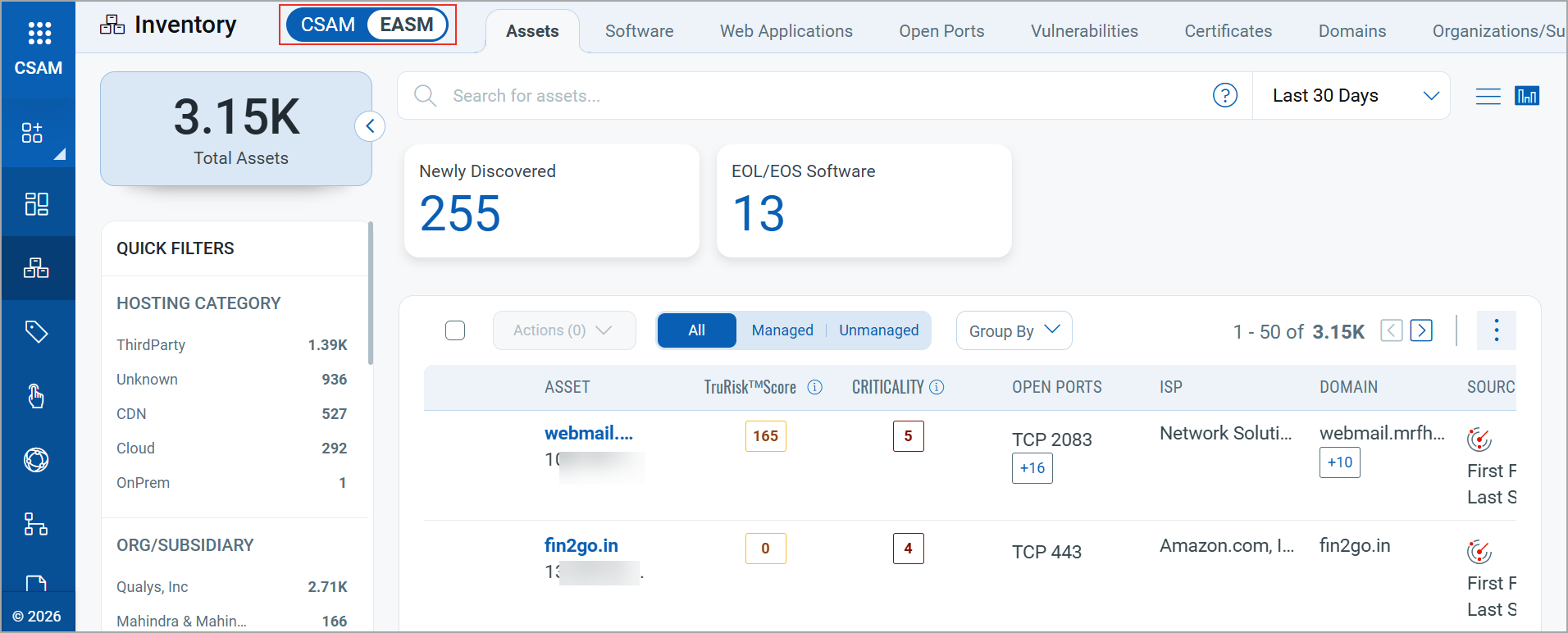
To access EASM, navigate to the Inventory tab and toggle the CSAM-EASM option to EASM.
Configure EASM Profiles
Get started by creating an EASM configuration profile.
System-Generated EASM Tags
When you configure an EASM profile, and the initial EASM discovery scan completes, the system automatically generates the following tags. These are system-defined tags and cannot be deleted:
- EASM
- EASM Confidence High
- EASM Confidence Medium
- EASM Confidence Low
- Shodan
- DNS SINKHOLE